NIST vs ISO 42001 vs EU AI Act — Explained Simply
Artificial Intelligence is moving faster than most companies can govern it. One week a business launches an AI chatbot, and
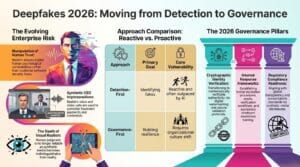
Deepfakes & Digital Trust: Governance Strategies for 2026
A few years ago, deepfakes felt more like internet entertainment than a serious threat. Viral celebrity edits, fake movie scenes,
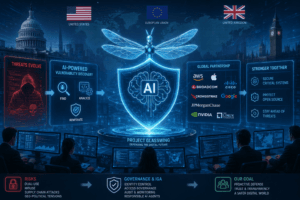
Anthropic Mythos & Project Glasswing: An IGA Architect’s Perspective on the AI Cybersecurity Frontier
Introduction The advent of advanced artificial intelligence (AI) models is rapidly reshaping the cybersecurity landscape. Among the most discussed developments

7 IAM Questions That Can Reveal Your Security Risk in Under 30 Minutes
You do not always need a three-month security assessment to understand whether an organisation has serious identity and access management
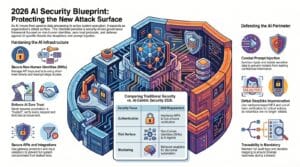
The 2026 Plan for AI Safety Using Rules as Protection
Now machines decide without waiting. They handle private details across huge systems. Because of that power, hackers aim there first.

Your Password Isn’t the Weakest Link Anymore. Your AI Agents Are.
For years, cybersecurity advice has been simple: use strong passwords and enable multi-factor authentication. That advice is still valid—but it’s

Seeing Is No Longer Believing: What a Buffett Deepfake Taught Me About AI Governance
The Day I Was Fooled by Warren Buffett I spent ten minutes watching Warren Buffett’s latest results before I realized
Agentic AI is Redefining Digital Identity
Agentic AI is transforming how work gets done. These autonomous systems plan, decide, act, and improve without requiring human input

The Role of AI in Enhancing Threat Detection and Response
Rapid advancements in technology are enabling cybercriminals to continually discover new methods to take advantage of weaknesses in digital systems.
Newsletters
Sign up with your email address to receive news and updates.